Analysis of Corrosion Process Development on Metals by Means of Computer Vision
DOI:
https://doi.org/10.4186/ej.2017.21.4.183Abstract
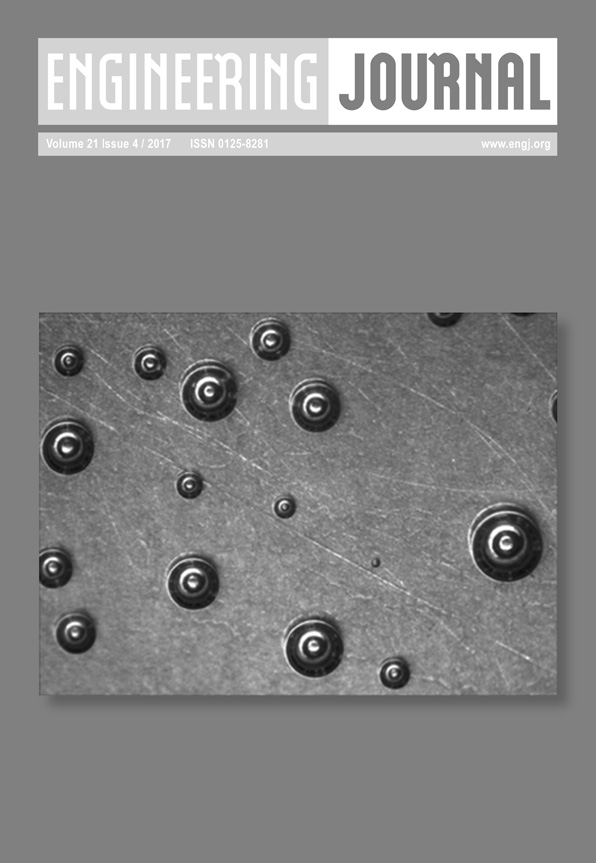
The paper deals with computer vision and image processing methods applied to the task of corrosion damage search. A step-by-step algorithm is given for processing of the data from a chemical corrosion experiment on a metal surface: image preprocessing, image binarization and identification of object contours, and analysis of object characteristics. The application of the developed methods is exemplified by detection and recognition of corrosion damage on a steel specimen, pitting corrosion, and corrosion of an aluminum specimen. Furthermore, the mechanism of fractal analysis for corrosion cracking specimens was studied and fractal dimension was selected as characteristics of corrosion damage.
Downloads

Authors who publish with Engineering Journal agree to transfer all copyright rights in and to the above work to the Engineering Journal (EJ)'s Editorial Board so that EJ's Editorial Board shall have the right to publish the work for nonprofit use in any media or form. In return, authors retain: (1) all proprietary rights other than copyright; (2) re-use of all or part of the above paper in their other work; (3) right to reproduce or authorize others to reproduce the above paper for authors' personal use or for company use if the source and EJ's copyright notice is indicated, and if the reproduction is not made for the purpose of sale.